Tumblr Is Full Of Phrases That We Are All So Desensitized To That They're Just Normal, But If You Say
tumblr is full of phrases that we are all so desensitized to that they're just normal, but if you say it to a person in real life its so funny to them its a one-hit insta kill
More Posts from Sumactic and Others





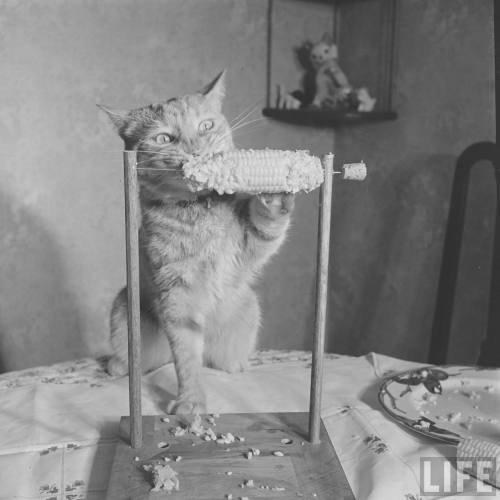

Cat eating corn-on-the-cob, 1951. Photos taken by Allan Grant for LIFE magazine.
stop i NEED that pic of the boy who took his cat to prom and she has a lil dress and is looking up at him with 100% love and tenderness……..

Cybercriminals are abusing Google’s infrastructure, creating emails that appear to come from Google in order to persuade people into handing over their Google account credentials. This attack, first flagged by Nick Johnson, the lead developer of the Ethereum Name Service (ENS), a blockchain equivalent of the popular internet naming convention known as the Domain Name System (DNS). Nick received a very official looking security alert about a subpoena allegedly issued to Google by law enforcement to information contained in Nick’s Google account. A URL in the email pointed Nick to a sites.google.com page that looked like an exact copy of the official Google support portal.
As a computer savvy person, Nick spotted that the official site should have been hosted on accounts.google.com and not sites.google.com. The difference is that anyone with a Google account can create a website on sites.google.com. And that is exactly what the cybercriminals did. Attackers increasingly use Google Sites to host phishing pages because the domain appears trustworthy to most users and can bypass many security filters. One of those filters is DKIM (DomainKeys Identified Mail), an email authentication protocol that allows the sending server to attach a digital signature to an email. If the target clicked either “Upload additional documents” or “View case”, they were redirected to an exact copy of the Google sign-in page designed to steal their login credentials. Your Google credentials are coveted prey, because they give access to core Google services like Gmail, Google Drive, Google Photos, Google Calendar, Google Contacts, Google Maps, Google Play, and YouTube, but also any third-party apps and services you have chosen to log in with your Google account. The signs to recognize this scam are the pages hosted at sites.google.com which should have been support.google.com and accounts.google.com and the sender address in the email header. Although it was signed by accounts.google.com, it was emailed by another address. If a person had all these accounts compromised in one go, this could easily lead to identity theft.
How to avoid scams like this
Don’t follow links in unsolicited emails or on unexpected websites.
Carefully look at the email headers when you receive an unexpected mail.
Verify the legitimacy of such emails through another, independent method.
Don’t use your Google account (or Facebook for that matter) to log in at other sites and services. Instead create an account on the service itself.
Technical details Analyzing the URL used in the attack on Nick, (https://sites.google.com[/]u/17918456/d/1W4M_jFajsC8YKeRJn6tt_b1Ja9Puh6_v/edit) where /u/17918456/ is a user or account identifier and /d/1W4M_jFajsC8YKeRJn6tt_b1Ja9Puh6_v/ identifies the exact page, the /edit part stands out like a sore thumb. DKIM-signed messages keep the signature during replays as long as the body remains unchanged. So if a malicious actor gets access to a previously legitimate DKIM-signed email, they can resend that exact message at any time, and it will still pass authentication. So, what the cybercriminals did was: Set up a Gmail account starting with me@ so the visible email would look as if it was addressed to “me.” Register an OAuth app and set the app name to match the phishing link Grant the OAuth app access to their Google account which triggers a legitimate security warning from no-reply@accounts.google.com This alert has a valid DKIM signature, with the content of the phishing email embedded in the body as the app name. Forward the message untouched which keeps the DKIM signature valid. Creating the application containing the entire text of the phishing message for its name, and preparing the landing page and fake login site may seem a lot of work. But once the criminals have completed the initial work, the procedure is easy enough to repeat once a page gets reported, which is not easy on sites.google.com. Nick submitted a bug report to Google about this. Google originally closed the report as ‘Working as Intended,’ but later Google got back to him and said it had reconsidered the matter and it will fix the OAuth bug.
the framing of generative ai as "theft" in popular discourse has really set us back so far like not only should we not consider copyright infringement theft we shouldn't even consider generative ai copyright infringement
really hate to do it but i'm locking all my works for the foreseeable future. the capitalistic, callous scraping of free, lovingly human-made art for the purpose of training generative ai is indescribably immoral, and goes against all i stand for as a writer who writes for the sake of it.
what i make is mine. i did that. and no cheap, synthesized, blended-up and watered-down pathetic pale mimicry can ever come close to what i can and have achieved.
i really, really hate to do this. a reader once commented and told me that my work was the reason they went and applied for an ao3 account. that exchange of respect and appreciation could not have happened if my works were locked from the start. i am fortunate to have felt this love for my work, and am sorry that i now have to sequester it.
what generative ai spits out is not art. there is no passion in the slop it regurgitates, no intentionality behind word choice or frustration with tense. no love imbued from hours spent hunched over a desk editing, no joy derived from having driven your friends crazy with the snippets you strategically dropped to deal the most emotional damage.
fuck generative ai and its profit-driven, uncaring, fuck-you practices. every new post about the violation of artists purely for their efforts to make art accessible sickens me. the industry needs to be better, and the individuals behind each model need to be better; every non-consensually scraped training set you weigh is worth a million artists' souls.
also, fuck anyone who says to stop writing a certain way because the llm "style" of writing is to use em-dashes and other such "tells" – the models do that because REAL LIFE HUMAN WRITERS do that. i will continue to use the goddamn punctuation. it was created to be used. don't be afraid to use it.

oh ok
Imagine if they find Luigi innocent and he has to go through the rest of his life as That Guy Who Got Turbodoxxed That One Time Because Everyone Thought He Was An Assassin.
-
 pluckyyoungdonna reblogged this · 1 month ago
pluckyyoungdonna reblogged this · 1 month ago -
 outofmyhead-justlikeyou reblogged this · 1 month ago
outofmyhead-justlikeyou reblogged this · 1 month ago -
 tryan-a-bex reblogged this · 1 month ago
tryan-a-bex reblogged this · 1 month ago -
 tryan-a-bex liked this · 1 month ago
tryan-a-bex liked this · 1 month ago -
 immtrash liked this · 1 month ago
immtrash liked this · 1 month ago -
 hay-is-gay liked this · 1 month ago
hay-is-gay liked this · 1 month ago -
 biahdv reblogged this · 1 month ago
biahdv reblogged this · 1 month ago -
 biahdv liked this · 1 month ago
biahdv liked this · 1 month ago -
 queenambrosine liked this · 1 month ago
queenambrosine liked this · 1 month ago -
 theladyofthedarkness reblogged this · 1 month ago
theladyofthedarkness reblogged this · 1 month ago -
 fantastic-cupcake liked this · 1 month ago
fantastic-cupcake liked this · 1 month ago -
 krystle-insert-blog-name liked this · 1 month ago
krystle-insert-blog-name liked this · 1 month ago -
 that0nelimebl00d reblogged this · 1 month ago
that0nelimebl00d reblogged this · 1 month ago -
 that0nelimebl00d liked this · 1 month ago
that0nelimebl00d liked this · 1 month ago -
 shadowedfye liked this · 1 month ago
shadowedfye liked this · 1 month ago -
 nebulainsel reblogged this · 1 month ago
nebulainsel reblogged this · 1 month ago -
 nebulainsel liked this · 1 month ago
nebulainsel liked this · 1 month ago -
 d3imoss liked this · 1 month ago
d3imoss liked this · 1 month ago -
 biolumin-escent reblogged this · 1 month ago
biolumin-escent reblogged this · 1 month ago -
 alexanderlightweight liked this · 1 month ago
alexanderlightweight liked this · 1 month ago -
 gayerthenthefourthofjuly liked this · 1 month ago
gayerthenthefourthofjuly liked this · 1 month ago -
 younggayanddoingokay reblogged this · 1 month ago
younggayanddoingokay reblogged this · 1 month ago -
 younggayanddoingokay liked this · 1 month ago
younggayanddoingokay liked this · 1 month ago -
 frogsmushroomsbutterflies reblogged this · 1 month ago
frogsmushroomsbutterflies reblogged this · 1 month ago -
 yupokaysuremhm reblogged this · 1 month ago
yupokaysuremhm reblogged this · 1 month ago -
 innerpolymathy liked this · 1 month ago
innerpolymathy liked this · 1 month ago -
 pockethep liked this · 1 month ago
pockethep liked this · 1 month ago -
 ghostrick-battlemaster reblogged this · 1 month ago
ghostrick-battlemaster reblogged this · 1 month ago -
 ghostrick-battlemaster liked this · 1 month ago
ghostrick-battlemaster liked this · 1 month ago -
 loveallfandoms1952 reblogged this · 1 month ago
loveallfandoms1952 reblogged this · 1 month ago -
 pan-left-close-on-the-steeple reblogged this · 1 month ago
pan-left-close-on-the-steeple reblogged this · 1 month ago -
 juicydangler reblogged this · 1 month ago
juicydangler reblogged this · 1 month ago -
 elizmanderson liked this · 1 month ago
elizmanderson liked this · 1 month ago -
 marble-reblogs reblogged this · 1 month ago
marble-reblogs reblogged this · 1 month ago -
 toph-proudfoot reblogged this · 1 month ago
toph-proudfoot reblogged this · 1 month ago -
 toph-proudfoot liked this · 1 month ago
toph-proudfoot liked this · 1 month ago -
 writer-or-whatever liked this · 1 month ago
writer-or-whatever liked this · 1 month ago -
 red-fox-of-zerk reblogged this · 1 month ago
red-fox-of-zerk reblogged this · 1 month ago -
 sarah-sandwich reblogged this · 1 month ago
sarah-sandwich reblogged this · 1 month ago -
 generictrashblog reblogged this · 1 month ago
generictrashblog reblogged this · 1 month ago -
 generictrashblog liked this · 1 month ago
generictrashblog liked this · 1 month ago -
 itsfreakingyouth liked this · 1 month ago
itsfreakingyouth liked this · 1 month ago -
 writer-or-whatever reblogged this · 1 month ago
writer-or-whatever reblogged this · 1 month ago -
 hawthorneox reblogged this · 1 month ago
hawthorneox reblogged this · 1 month ago -
 stargazing-enby reblogged this · 1 month ago
stargazing-enby reblogged this · 1 month ago -
 stargazing-enby liked this · 1 month ago
stargazing-enby liked this · 1 month ago -
 darechub liked this · 1 month ago
darechub liked this · 1 month ago -
 teratocybernetics reblogged this · 1 month ago
teratocybernetics reblogged this · 1 month ago -
 belphe9311 liked this · 1 month ago
belphe9311 liked this · 1 month ago




